Description:
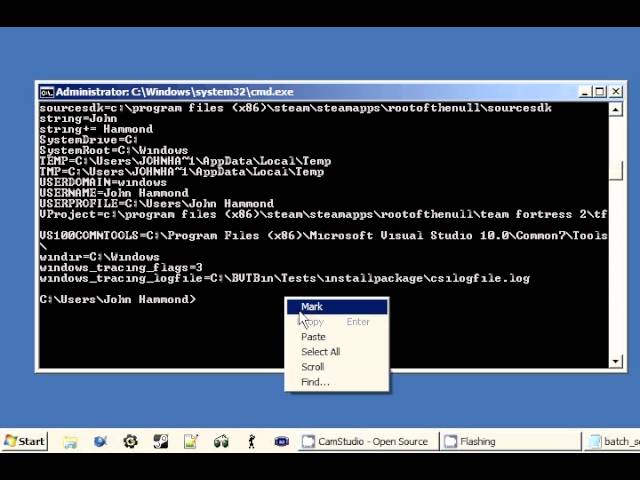
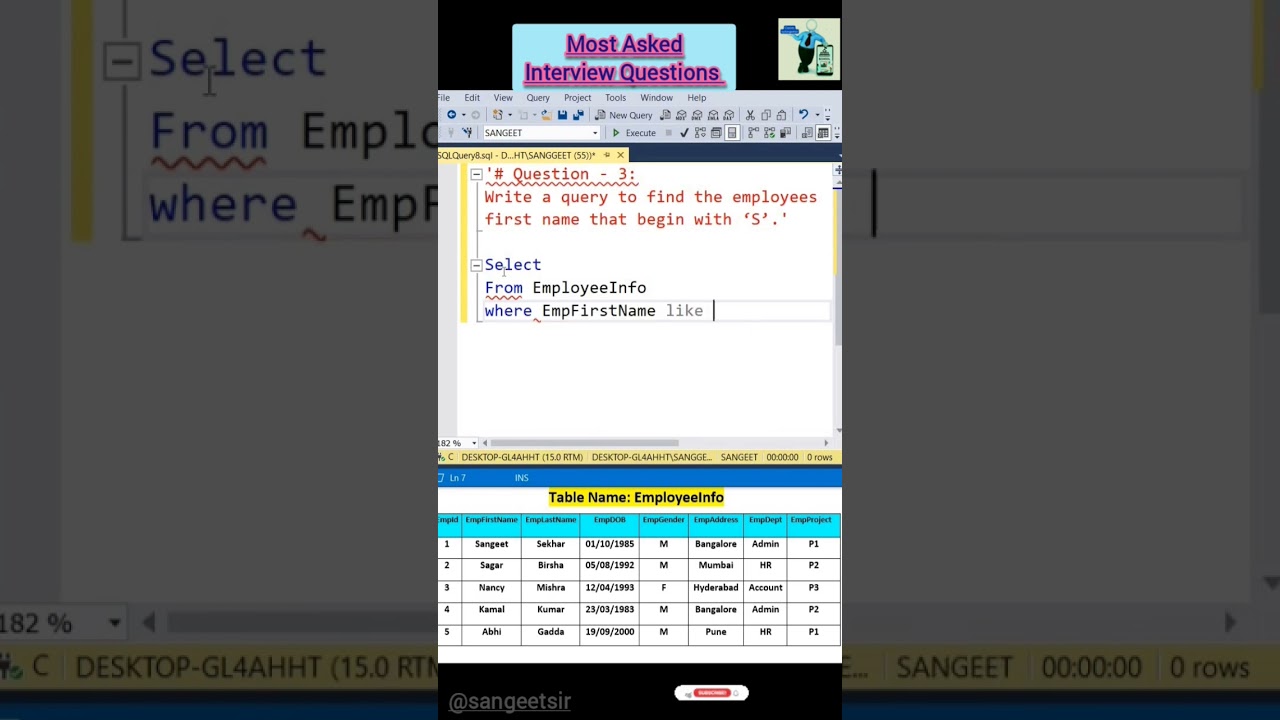
In this video, you’ll learn how attackers enumerate database table names and column names during SQL Injection exploitation. This step is crucial for extracting sensitive data once a vulnerability is confirmed.
We cover:
???? Manual SQLi enumeration
???? Using UNION-based payloads
???? Extracting DB schema
???? SQLMap enumeration commands
???? Protecting your database from schema exposure
Perfect for bug bounty hunters, ethical hackers, SOC analysts, cybersecurity students, and web security learners.
???? Tools Used: Burp Suite, SQLMap, Kali Linux
???? Topic: Web Application Security | OWASP Top 10 | SQL Injection
This video includes:
✔ UNION-based enumeration
✔ SQLMap schema discovery
✔ Extracting table & column names
✔ Practical step-by-step examples
???? QUESTION:
Which SQL Injection topic should I cover next?
– Dumping credentials
– Bypassing login pages
– WAF evasion payloads
Drop your choice ????????
LIKE • SHARE • SUBSCRIBE for more cybersecurity content! ????
#SQLInjection #Enumeration #EthicalHacking #BugBounty #Pentesting #DatabaseSecurity #WebSecurity #OWASP #CyberSecurity #HackingTutorial #infoseccommunity
Share this link via
Or copy link